With the acceleration of digital transformation, cloud computing has become an indispensable part of the enterprise information technology architecture. As an important digital economy in Southeast Asia, Malaysia has a rapid development momentum for its cloud servers. This article will conduct in-depth analysis of the security and stability of Malaysian cloud servers, helping enterprises make informed decisions when choosing cloud services.
Security overview of Malaysia Cloud Servers
The security of Malaysian cloud servers is mainly reflected in data protection, access control and compliance. First, many cloud service providers use advanced encryption technology to ensure the security of data during storage and transmission. These technologies include SSL/TLS encryption and data at rest encryption, which can effectively prevent data leakage and illegal access. In addition, cloud service providers often implement multi-level access control policies to ensure that only authorized personnel can access sensitive data.
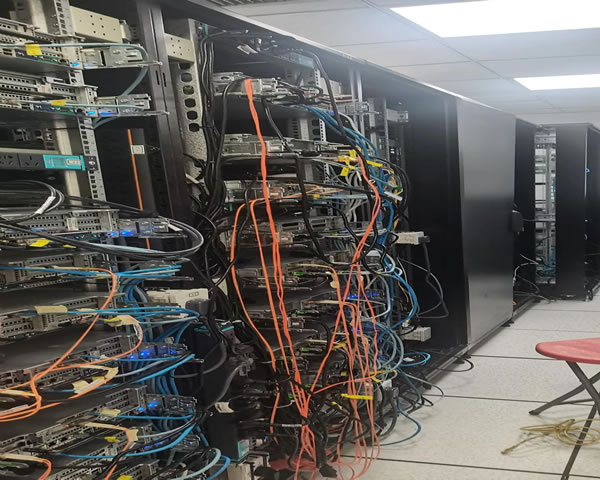
Physical security of data centers
In addition to cybersecurity, Malaysia's cloud service data centers are also worthy of attention in terms of physical security. Most cloud service providers have 24-hour monitoring and security personnel in their data centers, equipped with advanced intrusion detection systems and biometric technologies. These measures greatly reduce the risk of physical damage and theft. In addition, data centers are often located in areas with low natural disaster risks, which further enhances their safety.
Stability analysis of cloud servers
The stability of Malaysian cloud servers depends mainly on the reliability and redundant design of their infrastructure. High-quality cloud service providers will adopt a high availability architecture to ensure uninterrupted service operation through load balancing, automatic failover and other technologies. In addition, Malaysia's network infrastructure is constantly improving, and the coverage of fiber optic networks has increased year by year, which has significantly enhanced the connection stability of cloud servers. Together, these factors ensure the continuity of the business of the enterprise.
Data backup and recovery mechanism
During the use of cloud servers, data backup and recovery mechanisms are one of the important criteria for evaluating their stability. Malaysian cloud service providers usually provide a variety of backup solutions, such as full backup, incremental backup and off-site backup, to ensure that data can be quickly restored in the event of an accident. These backup solutions not only improve data security, but also provide enterprises with business continuity guarantees.
Compliance and legal guarantees
With increasingly stringent data privacy regulations, compliance has become an important consideration for enterprises when choosing cloud servers. Malaysia has clear laws and regulations on data protection, such as the Personal Data Protection Act (PDPA), which requires cloud service providers to follow certain standards when processing personal data. These legal guarantees provide additional security for enterprises to ensure that they do not violate relevant laws and regulations when using cloud services.
Technical support and service response
Finally, the technical support and service response speed of Malaysia's cloud servers also affect its security and stability. Most cloud service providers provide 24/7 technical support to ensure that problems can be responded and resolved in a timely manner. This kind of service can not only ensure the normal operation of the enterprise, but also enhance the enterprise's trust in cloud services and further improve security and stability.
Summary and suggestions
To sum up, Malaysian cloud servers have obvious advantages in security and stability. When choosing cloud services, enterprises should focus on factors such as data protection, physical security, network stability and compliance. It is recommended that enterprises carefully understand their security measures, service agreements and technical support when evaluating cloud service providers to ensure that they choose the cloud server that best suits their needs. At the same time, regular review and updates of your own security strategies can only remain competitive in a rapidly changing digital environment.
- Latest articles
- How Do Enterprises Evaluate The Role And Cost Of Hong Kong And Singapore Cn2 In Multi-regional Cdn?
- Summary Of Questions And Answers: How Much Does Server Hosting Cost In The United States? How To Reduce Long-term Expenses?
- Overseas Deployment Considerations: How To Choose A Thai Cloud Server To Avoid Pitfalls
- Based On Industry Cases, Analyze The Uses Of Hong Kong Cloud Servers And The Advantages Of Deploying Them In Multiple Regions
- Things To Note When Purchasing Native Ip In Vietnam Include Bandwidth, Asn And Service Provider Evaluation Indicators
- Where To Buy Japanese Servers? Payment Method Security And Refund Policy Instructions
- Analyze The Advantages And Disadvantages Of Overseas Vps Malaysian Nodes From The Perspective Of Cost And Delay
- How To Find Hong Kong’s Native Ip Optical Computing Cloud? Detailed Channels And Precautions
- Csgo National Server Shows Possible Operation And Maintenance And Hardware Issues Behind Korean Server Maintenance
- Practical Experience Sharing: How Long Does It Take To Change To A Thai Server? How Does It Affect The Ranking Time And Method?
- Popular tags
-
What You Need To Know Before Buying A Malaysian Cloud Server
before buying a cloud server in malaysia, it is very important to understand some key elements. this article will give you a few key points you need to know before buying. -
How To Choose A Cloud Server Suitable For The Malaysian Market
this article details how to choose a cloud server suitable for the malaysian market, including performance, price, security and other considerations. -
Things To Note And Tips For Renewal Of Vps In Malaysia
Understand the precautions and tips for renewing VPS in Malaysia, help you make wise choices and ensure the stability and security of your website.


